Karl Robinson
March 25, 2026
Karl is CEO and Co-Founder of Logicata – he’s an AWS Community Builder in the Cloud Operations category, and AWS Certified to Solutions Architect Professional level. Knowledgeable, informal, and approachable, Karl has founded, grown, and sold internet and cloud-hosting companies.
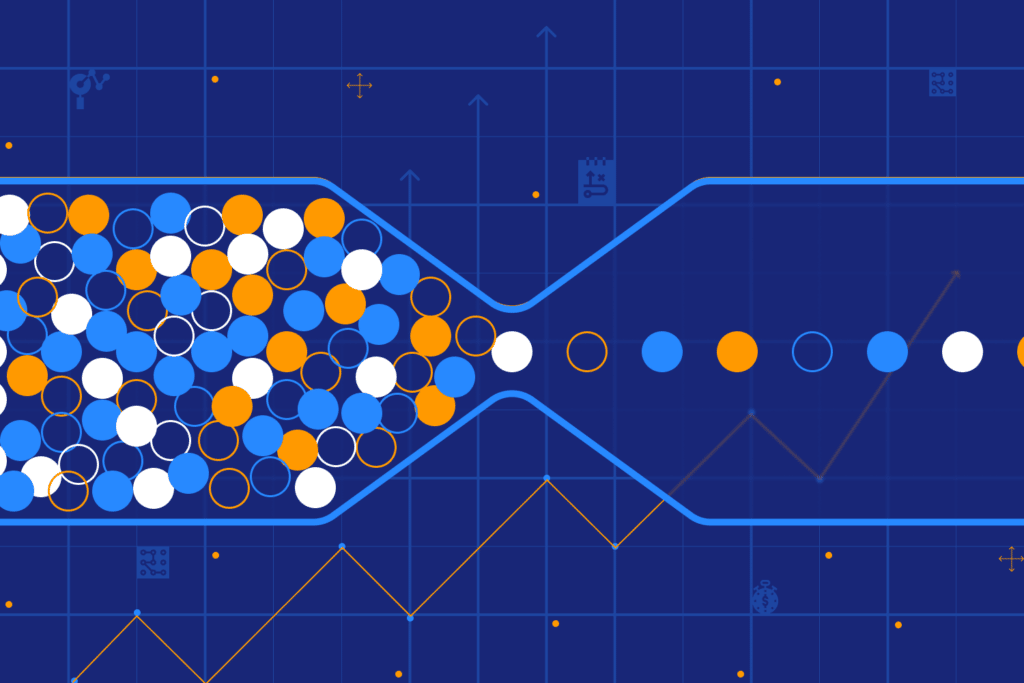
AWS security fails when organisations treat it as a setup task instead of an ongoing operational responsibility.
As cloud environments grow, organisations make more access decisions and struggle to keep monitoring precise. Over time, security standards drift away from what they were originally meant to enforce.
Temporary permissions can remain in place. Monitoring can produce noise instead of insight. Delivery pressure can push security work aside.
Why Do Identity and Access Controls Break Down as AWS Environments Grow?
Access models that work early on often start to break down as organisations scale. What begins as pragmatic flexibility often becomes long-term exposure.
As environments expand, access decisions are made more often and under tighter time pressure. You usually see this in a few familiar ways:
- Permission boundaries loosened to unblock work and left in place once delivery moves on
- Exceptions created for speed becoming part of the default access model
- Temporary access persisting because ownership is unclear or review capacity is limited
At scale, volume can significantly increase risk. Without regular review and enforcement, access rules slowly become more permissive.
As organisations grow, clarity over who can access what is often lost before direct control of access itself is lost. Permissions granted months earlier can remain in place because ownership is unclear or review capacity is limited. Without this visibility, organisations accumulate access risk even when no single decision appears unsafe.
Within an established AWS security environment, organisations often find that periodic audits no longer reflect real risk. Cloud platforms often change fast enough that point‑in‑time checks can fall out of date. New resources appear, permissions evolve, and configuration settings shift as delivery accelerates. Without continuous validation against defined baselines, your AWS environment can drift while reports lag behind current conditions.
How Configuration Drift Undermines AWS Security Over Time
Configuration drift can contribute to persistent and less visible security problems in AWS environments. Even when strong standards are defined initially, they are difficult to maintain under ongoing change.
Manual adjustments and urgent fixes build up over time, usually applied to solve immediate problems and then left in place once the pressure passes. Common patterns include:
- One-off changes applied during incidents and never revisited
- Environment-specific exceptions copied forward release after release
- Configuration decisions surviving long after their original context is lost
Each change may be justified in isolation, but together they weaken the overall security posture. Platform owners often struggle to determine which configurations remain intentional.
Configuration settings directly influence the level of risk present in an environment. Mature programmes define, document, and monitor these settings to keep standards effective. Some organisations use external AWS security and operations support to help sustain this work, for example through ongoing AWS managed services.
As drift builds up, data protection problems start to surface.
Pause point: If this pattern feels familiar, it usually indicates that AWS security ownership is no longer keeping pace with change. Logicata supports organisations at this stage, helping stabilise security controls and restore visibility as environments grow. Talk to a Logicata AWS expert →
Encryption sets a baseline, but configuration drift and access sprawl determine who can reach sensitive data in practice. As platforms grow, data can spread across services and storage layers before ownership, classification, and access expectations are updated. Permissions can linger, storage configurations can age, and organisations can lose confidence in their ability to prove control.
When drift obscures intent, assumptions collapse under scrutiny.
Why AWS Security Ownership Breaks Down Under Delivery Pressure
One of the most significant AWS security risks sits in how work is structured, not in the technology itself. Security responsibilities sit alongside delivery work and incident response, compete for limited attention, and face the same delivery timelines.
Responsibility becomes concentrated in a small number of experienced individuals, creating fragility and burnout. When those individuals are unavailable, security posture can degrade.
Long-term AWS security depends on clear ownership and the ability to keep security work moving without slowing delivery.
Five governance questions that expose AWS security gaps
- Can access to sensitive data be proven today, not just defined in policy?
- How quickly would configuration changes that introduce exposure be detected?
- Which security controls depend on individual knowledge rather than shared processes?
- Where has the security baseline drifted across accounts and environments?
- What security work stops happening during delivery pressure or staff absence?
These questions reflect how AWS encourages teams to think about security maturity through ongoing assessment of design, ownership, and operational resilience. One‑off technical decisions do not sustain security.
AWS Security Is an Operating Model Decision
Most organisations can define AWS security practices clearly. Sustaining them over time is much harder. As platforms grow and change accelerates, operational pressure widens the gap between what teams intend and what actually happens.
Over the long term, security outcomes depend on how organisations govern access, monitor change, and share responsibility.
For many organisations, maintaining strong AWS security comes down to an operating model decision. Organisations either absorb security into an already stretched internal function or treat it as a continuous, dedicated capability alongside platform operations.
This is where working with an experienced AWS partner becomes relevant. Expert AWS managed services can help organisations sustain security controls, governance, and visibility as environments grow, without relying solely on periodic fixes or individual effort.
Continue the Conversation
If this reflected challenges you recognise, a short conversation with our AWS expert can help you sense‑check priorities and pressure‑test assumptions in your own environment.